In part 1, I explained how ClearPass Social Login using OAUTH works in depth. In this part, I will explain how to configure it based on Azure AD. In brief, you need to configure
- Azure: To register an app (Get Client ID / Secret)
- ClearPass: To configure a web login page with Social Login + Service to handle the guest authentication
- Controller: To assign devices initial role with captive portal page pointing to ClearPass + a role after successfully authenticating
Let’s start with Azure configuration first.
Azure Configuration
Step 1: Login to Azure Portal and search for App registration. Register an app and provide the Redirect URI to point to ClearPass Guest page (to be created on ClearPass)

Step 2: Select Certificates & Secrets and then create a new Client Secret. Specify the validity as you see appropriate.


Step 3: Copy the secret key that is provided and save it in a secure manner (the one shown below is already deleted)

Step 4: Copy the client ID for this application from the overview tab.

Step 5: Now the only remaining part is provide the app the needed permissions. Navigate to API permissions, select Microsoft Graph and add Directory: Read All


Steps 6: Grant the app the permission to read directory data (Grant admin consent)

The above concludes the config needed on Azure side. Let’s configure ClearPass side now.
ClearPass Configuration
Step 1: Create a Guest Web Login Page, Add Social Login Option and select Microsoft Azure AD. Make sure to specify the post back address to point to the certificate common name that is installed on your controllers.


Step 2: Specify the client ID and client secret based on the values you obtained while setting Azure App (Steps 3 and 4 in Azure configuration section)
Step 3: Enable Group membership fetching if needed in your workflow

Step 4: Configure a Service using the Guest Template (Cloud Identity/Social Media Authentication)

At the below screen, keep the default values for now. In the next step, we will change them to azure.
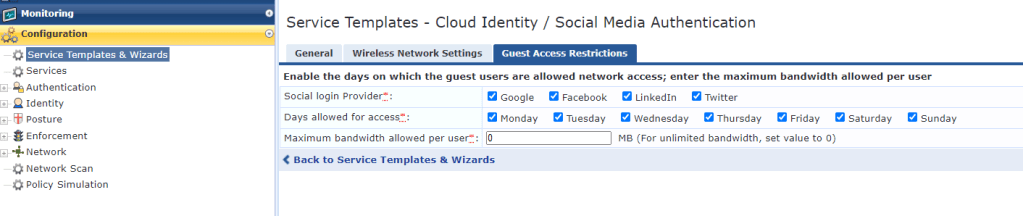
Step 5: Change the social login provider in the created policy to azure. Remove the other conditions that are not used.

This completes the configuration from ClearPass side. Just make sure Clearpass has internet access via https to reach Azure graph APIs.
Now let’s check the controller configuration.
Controller Configuration
Controller needs to be configured with an initial role that is linked to a Captive portal profile which redirects traffic to ClearPass. The minimal needed policies for this role are listed below.

Below is a sample configuration for this role.
netdestination microsoft_whitelist
name *.microsoft.com
name *.microsoftonline.com
name login.microsoftonline.com
name *.aadcdn.microsoftonline-p.com
name login.live.com
name mbs.microsoft.com
name go.microsoft.com
name login.microsoftonline-p.com
name secure.aadcdn.microsoftonline-p.com
name urs.microsoft.com
name auth.gfx.ms
name dynamicscrmemea.accesscontrol.windows.net
name sc.imp.live.com
name *.windows.net
name *.passport.net
name *.crm4.dynamics.com
name home.dynamics.com
name cloudredirectoreur.cloudapp.net
name cloudredirectoreursec.cloudapp.net
name *.azureedge.net
name www.crmdynint.com
name graph.windows.net
name aadcdn.msauth.net
!
netdestination clearpass_cp
name
host
!
netdestination allowed_dns_servers
host 8.8.8.8
!
ip access-list session restricted_dhcp
user any udp 68 deny
any any svc-dhcp permit
!
ip access-list session restricted_dns
any alias allowed_dns_servers svc-dns permit
!
ip access-list session custom-logon-control
any network 169.254.0.0 255.255.0.0 any deny
any network 240.0.0.0 240.0.0.0 any deny
!
aaa authentication captive-portal "PGUEST_cp_prof"
server-group ""
redirect-pause 3
no logout-popup-window
login-page ""
no enable-welcome-page
white-list "clearpass_cp"
white-list "microsoft_whitelist"
redirect-url "https://www.arubanetworks.com"
!
user-role p-guest-logon
captive-portal "PGUEST_cp_prof"
access-list session global-sacl
access-list session restricted_dhcp
access-list session restricted_dns
access-list session apprf-p-guest-logon-sacl
access-list session custom-logon-control
access-list session captiveportal
!Make sure to associate this initial role to the AAA profile associated with the VAP. This is a simplified configuration for the controller.
I hope this is useful. Feel free to share your comments and feedback. If you are interested to check other ClearPass Tiny Bites, click here.
Hi Ayman
I refer to part2 configuration, there is an error.
“The reply URL specified in the request does not match the reply URLs configured”
Is the url of step 2 of the part2 clearpass configuration rigth?
wait for your reply,
Thanks
LikeLike
Hi,
The URL needs to be changed to reflect your ClearPass installation… This was the URL used in my demo environment, you need to change it based on your ClearPass setup.
LikeLike
For some reason following these instructions when I launch the web portal I get an error and no Azure sign in option. Any ideas what I’m missing? The error is “Required field unavailable”.
Thanks
LikeLike
How are you testing? You were connected to WiFi and testing or are you manually trying to open the URL?
LikeLike
Launching it from the Clearpass config page. From configuration->Web Logins->Launch button.
LikeLike
Hi Ryan,
It will not work as such as the Aruba controllers will append the mac-address field in the redirection URL. This is missing when you launch it directly..
In your case, you need to append to your url and add ?mac=00:00:00:00:00:00 if you want to simulate it directly without being connected to Aruba controllers..
LikeLike
i got the blank page after redirect to login.microsoft.com
LikeLike
Hi Sandi,
So the Microsoft login page was loaded? If not, did you add the whitelist entries?
Can you share a screenshot?
LikeLike
I’m having a similar issue as Sandi here is a screen shot of what I get after I click on the Azure login icon.
https://imgur.com/a/ZKZhC4E. I did verify that the network can get to the azure portal. I’m also using an IAP cluster vs a controller but I did whitelist all the same urls and IP addresses. Any help would be appreciated.
LikeLike
Hi Ryan,
Are you sure you put the right ClearPass URL?
LikeLike
Hi Ayman,
Thank you for this great guide! One question: do you know if it is possible to use Azure B2C Accounts for authentication? I can not adjust the authentication and access token url.
Thanks,
Reto
LikeLike
Hi Reto,
I expect this to work as well with B2C accounts but I think you will need to create your app registration under that B2C tenant.. I didn’t try it before though..
LikeLike
Hi,
We’ve also followed your instructions from parts 7-8.
When a client connects to this open SSID, the client redirect to a Windows login page (OAuth2). However, there is an issue like this, which you can see in the URL.
Could you please check how to fix it?
Best Regards,
Suphat.
LikeLike
Hi Suphat,
I can’t check external links.. Please specify what is the error you are getting to try to help you..
LikeLike
Hi Ayman,
Unfortunately, when I was paste link URL from Google Drive but it disappear.
The error I found was AADSTS9002325: Proof Key for Code Exchange is required for cross-origin authorization code redemption.
LikeLike
Hi Suphat,
Can you please specify how you created your application on Azure? You need to create it under web not single page application
Check this link for details https://stackoverflow.com/questions/64692600/aadsts9002325-proof-key-for-code-exchange-is-required-for-cross-origin-authoriz
LikeLike